
How we discovered a Ukranian cybercrime hotspot
Our researchers wanted to take a closer look at the GandCrab ransomware. Then they found an entire cybercrime network, operating from Ukraine.

How we discovered a Ukranian cybercrime hotspot
Our researchers wanted to take a closer look at the GandCrab ransomware. Then they found an entire cybercrime network, operating from Ukraine.
Of mortal domains and cars without admins
From 3 to 5 October, the IT security industry met in Montreál, Canada, for the annual Virus Bulletin Conference. Tim Berghoff was there for G DATA.

Messenger: Whatsapp vulnerability threatens billions of users
A vulnerability in Whatsapp can currently only cause the app to crash. However, criminals could further develop the current exploit for malicious purposes. We provide an overview of the situation.
Next-Generation Antivirus: How G DATA can protect customers from unknown threats
Antivirus programs no longer only work with malware signatures. Read about the next-generation technologies G DATA uses and how you can benefit from them.
Android Trojan reads Whatsapp-Messages
A spyware still in development can read users Whatsapp-Messages and other sensitive data. G DATA researchers analysed the Malware to protect our customers.
Botnet: No jailtime for Mirai-creators
Their IoT-botnet created damage worth 100 Million US-Dollars. Yet, the developers will serve no jailtime - because they cooperated with the FBI.

Interesting approach: Skill Squatting with Amazon Echo
Mishearing something every once in a while is a normal thing for humans. In that respect, Amazon Echo has some human characteristics as well. A research team from the University of Illinois has taken a closer look at Echo, Alexa and the abuse potential for malicious Alexa skills. They have presented…
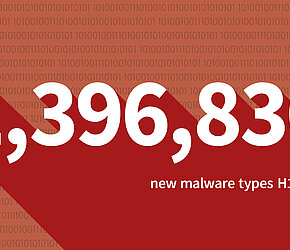
Malware figures for the first half of 2018: The danger is on the web
More often than not, today's malware is distributed via the web – executable files are becoming less of a problem. Also, the G DATA security experts were able to identify a particular trend in the first half of the year that targets users' computers.
Story Point based Cost Estimation
Story points are popular in agile software development to estimate the work, complexity and risk of backlog items. This post discusses an idea to utilize the story point estimations to compute the costs of a project.

The true cost of bad IT security
Investments in IT security are difficult for many companies, mainly because their economic benefits are not always easy to calculate. Current examples show that this can quickly become expensive, as the producer of the iPhone chips had to experience for himself.